Similar Books in Computers & Internet
View All Similar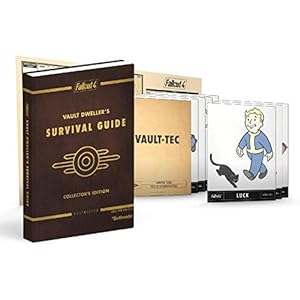
Fallout 4 Vault Dweller's Survival Guide Collector's Edition: Prima Official Game Guide

Fallout 4 Ultimate Vault Dweller's Survival Guide Bundle

#AskGaryVee: One Entrepreneur's Take on Leadership, Social Media, and Self-Awareness

The Hundred-Page Machine Learning Book

Instant Access Databases
Typographics 3: Global Vision